Wazzup:
Ok, so I have this small fascination with having downloaded the Internet, so in my life, I have found that Bit Torrent used in a semi-legal way is a great tool. Since I’m paying more child support than what any child needs, I have to cut where it doesn’t really matter and TV is the start. So between watching lots of ROKU and downloading/watching TV shows/movies… I have found that I can pretty much watch anything anyone else does, but it might be a day or so later. Not to mention listen and play whatever I want, but that’s a different story.
The Setup:
Charter was gracious enough to give me one heck of a deal to replace my outdated worn out 5mb ATT DSL Line (though it was one stable and reliable services… Thank you ATT). I spied Charter for a long time and found a deal I couldn’t go wrong with, $50 install, $200 modem, $200 rebate on Modem and $50 rebate on install, with a $29/mo fee for a whopping 40Mb/Sec, of course that’s only for 6 months, then its $50/mo, which is what I was paying ATT for. Nice deal on my side and I get +35mb/sec for about $2/mo. WOW.
The Issue:
Trying to update large list of torrent files with some “friends” I started to notice that once I changed to charter I could either surf the Internet OR download torrents. At first I didn’t quite catch what was going on, as I figured it had something to do with the speed I had and how much I was downloading, but it started to be a PITA so I decided to tackle the task of finding out why if uTorrent was running, I had to pause them to browse the Internet. So just to get some keywords out there: Can’t browse the Internet while uTorrent is running on Charter Service with Motorola Modem but pings and other devices and/or computers work just fine.
Research:
So as any good person that knows how to Google, I started with some generic Google searches.
Some people were complaining about the same thing but most blamed the modem or the router.
So I decided to rule that out, I’d remove my Router and just plug into the modem. At the same time, I’d connect a laptop (2nd computer) and just verify that it couldn’t be the modem. So I fire up the laptop, my phone, a tablet, another phone and connect to the wifi. Then on my desktop I fired up uTorrent then WHAM… Desktop looses IE (started to think TCP) connection but the rest of the computers were just flying. Not the modem, if it was going to be the modem, my other devices would have died also.
Some people blaming uTorrent.
Not really wanting to leave uTorrent (as it was required for one of my “friends” sites) I found another compatible torrent program. qTorrent, surely it’s something with the torrent program…. Right? Well after learning a much less featured and slower program (man qTorrent takes forever to load), I was surely surprised to find that it was the program. Here we go with the real tech work.
Some posts pointed at the TCP sessions were being exhausted.
This is a fair statement. If I were to give one session/files (not torrent). The program would surely use over 65,000 connections. So off to the CLI.
nbtstat –an
Not really an impressive number came back, so I put that idea on the back burner, though it made sense.
Finding it was a TCP session issue… A breakthrough?
I don’t know if it was any sort of breakthrough, but it was however a great way to start testing and find when the issue happened. But how to test a TCP session? Pings always worked, even when the Internet was running, but that’s ICMP and Bit-Torrent kept running, but that’s UDP traffic. For those that don’t get this part, skip So I figure if the UDP works, ICMP works, then TCP has to be the issue. Found this nice little utility here, big thanks to Eli Fulkerson! This tool allowed me to start a continuous "ping” to a TCP port, which I used 80 and 3389, just to make sure it wasn’t an issue with HTTP browsing but more like an issue with TCP connections.
So I figure if the UDP works, ICMP works, then TCP has to be the issue. Found this nice little utility here, big thanks to Eli Fulkerson! This tool allowed me to start a continuous "ping” to a TCP port, which I used 80 and 3389, just to make sure it wasn’t an issue with HTTP browsing but more like an issue with TCP connections.
Sure enough, it was a TCP session issue where once uTorrent, now qTorrent started, it blocked all TCP sessions, but why?
How to diagnose TCP Sessions and why they were failing.
Using Netstat –abn and Resource Monitor built into Windows 7, I found that there were no obvious issues. Back to the research board…
Tweaking TCP for broadband….
Surely this was it, it made so much sense. I get faster Internet, I have more bandwidth, it has to be TCP settings to low for my new bandwidth (NOW… AFTER ALL OF THIS, IT DOESN’T MAKE AS MUCH SENSE, but I was desperate) I used this utility here TCPOptimizer. Had some nice settings some seemed legit, so after a reboot, I fired up my test (which had become, TCPPing, qTorrent and 3 minutes of waiting at this point). And WHAM… it works.. yay, I’m at 3 minutes, still working, 5 minutes… Still working.. YAY, I’m about to write a nice UTM blog on this until… Death to my TCP. So maybe that didn’t fix it. I’ll leave the boring tweaking settings out of this blog, because it’s already long enough, and IT’S STILL NOT FIXED.
Maybe some Crazy Filtering/RST bomb from Charter?
I started to think maybe this was some reverse attack against P2P traffic. It didn’t’ make much sense, but… either did anything else. I found this site that confirmed they don’t much care…. on to the next idea.
I got it… Ethernet Driver
Of course, I’m such an idiot… It’s an issue with the Ethernet driver, I have to update it, that will fix my world. The driver had to be at least 6-12 months old, I’m running a new bit-torrent client… yadda… yadda. That’s it, my driver was almost a year old, of course… Download, Install, Update, Reboot, Wham… Bam… Damn, that wasn’t it.
Dedicating my upcoming life to fixing this issue… ONE WAY OR ANOTHER.
Ok, it didn’t take that long, but I had decided that this was a me against the machine. Nobody on the Internet had a clue, forums were spread with similar, less technically detailed questions, with the same answers I’ve tried 5 paragraphs up. So, if it took me a case with Microsoft (yes I’d have thrown a Microsoft Partner Case at it), I will do it.. DAMN IT!
The Fix (almost but not quite):
Starting from what I know
I know that it has to do with TCP Sessions, I know it has to do with running bit-torrent applications and I know there are no logs or known signs of the reason it was failing both on the routers and computer… That was just about it.
Lets go from what it’s not
- I know it’s not the version, application, driver, etc…
- I know it’s not the router being “junk” like I kept reading
- I know it’s not my version of Windows being corrupt (ran SFC /scannow)
- I know it’s not possible this is happening to me, I am IT.
The start of thinking and breaking into this is critical at this point. My sanity depends on it.
Time to consult my consultant… You might know him as Yarbi say what?, but I know him as a super smart dude I respect and we both bounce ideas off each other to come up with some real good solutions to real world scenarios (not all technical). We are still working on Vacation Return Policies.
New network card… This should rule a lot out
After talking with Yarbi over lunch, I decided that it almost had to be my Network card. It was really the only thing that made sense. Yarbi just happened to have a decent PCI 100/1000 NIC that was sitting on his shelf. I must borrow.
Installation… I noticed this was another Realtek card, but heh, what can it hurt. Reboot, change the patch cable. BAM, (Like it blew up).. NOGO, back to the drawing board.
The Fix.. Yes a FIX
I really hope this helps someone out, going to quickly outline the issue, what I know it is not and what the fix was. This could possibly apply to many routers, but the screenshots I’m going to include are from a Motorola Surfboard. Having seen lots of modems in my IT history, I know this setting is on A Lot of them. I hope this helps.
- Issue with TCP connections, including HTTP when Bit Torrent Application running.
- ICMP (Ping) and UDP (Bittorrent) are not affected
- It only affects the computer bittorrent is running on, it does not affect the other devices on the exact same network and Internet connection.
- Drivers updated and no virus present.
Drum Roll…
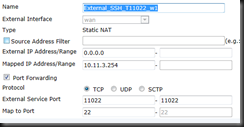
Accessing the Motorola Surfboard modem.

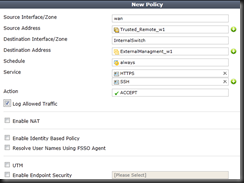
There it is. The two options in question were:
- Port Scan Detection
- IP Flood Detection
Disable both, make your screen look like this and it should resolve your issues. I really hope this helps someone out there!
It all makes sense. Damn, why didn’t I think about this 16 hours ago.
Post Analysis
Now that we know the issue was Port Scan Detection and/or IP Flood Detection. What do they do. Do we need them? Why turn them off? Why does Bit Torrent trigger these. Well here we go, from my Security Mind.
Port Scan Detection (disable)
This is defined as: “Port Scan Detection detects and blocks port scan activity originating on both the LAN and WAN”
What does this mean for P2P apps? Well, P2P creates a lot of outbound connections to multiple destinations, those destinations return the favor and then some by trying to spread the joy of P2P (the reason it works). This quick spread of P2P reconnects look like a Port Scan because of the large quantity of return ports that each destination returns. Also from the inside it is possible that the P2P application is triggering it due to the large quantity of ports is uses to communicate, but it is more likely on the WAN side.
IP Flood Detection
This is defined as: “IP Flood Detection detects and blocks packet floods originating on both the LAN and WAN”
But why does P2P trigger this effect, well, it’s really likely that the either LAN or the WAN could be blocking these large quantities of P2P connections that connect to many sources, seed in many directions and just plain out look like a flood of IP type traffic.
So why does UDP, P2P and ICMP work.
UDP is connectionless and would be very hard to close a connection with, it could be denied but the way I was testing UDP was with the P2P client, which would have had connections to the destination servers before the protection kicked in and dropped the new connections, but… it is also possible that the firewall can only truly block TCP sessions, I don’t really want to spend hours figuring this out, there is likely some manual or blog about this, I just haven’t found one.
Enjoy, now I can surf and P2P all at the same time… YAY!